 You might remember Bitcoin, the cryptocurrency known for increasing the anonymity and privacy of transactions on the web. Bitcoin was gaining ground for a while, but a couple of key events left it in the dust, sinking to seeing use only as a currency used by hackers and criminals in online black markets. Now, however, it seems that Bitcoin is being used again, and with a few key innovations in how it’s spent, Bitcoin will continue to grow more popular as a payment option.
You might remember Bitcoin, the cryptocurrency known for increasing the anonymity and privacy of transactions on the web. Bitcoin was gaining ground for a while, but a couple of key events left it in the dust, sinking to seeing use only as a currency used by hackers and criminals in online black markets. Now, however, it seems that Bitcoin is being used again, and with a few key innovations in how it’s spent, Bitcoin will continue to grow more popular as a payment option.
WIRED magazine reported on the fall of Bitcoin, stating that it can be directly attributed to two major events: 1) the fall of Mt. Gox, a major Bitcoin exchange, and 2) the fall of Silk Road, the online drug trafficking market for which Bitcoin was heavily utilized. Mt. Gox, which was based in Tokyo, Japan, was responsible for handling nearly 70 percent of all Bitcoin transactions. An immense hacking attack rendered Mt. Gox bankrupt following the disappearance of over $450 million worth of Bitcoins, some of which were stolen. Mt. Gox was forced to declare bankruptcy in 2014. Authorities claim that the screw-up was caused by a relative lack of management and experience, as well as an overwhelming amount of apathy toward the business.
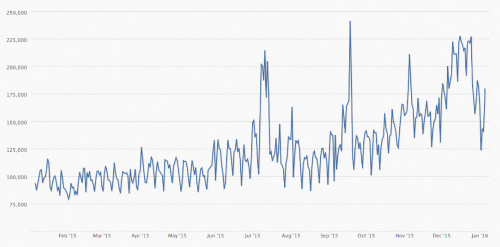
That’s a ton of missing Bitcoins; well over 850,000. What’s shocking, though, is that nobody knew where they went for the longest time. Some were stolen and recovered over time, but the fact remains that a $450 million heist is enough to cripple even the most profitable company. Considering how Bitcoin is so often associated with scandal and corruption, you’d think it would have sunk into the past. Yet, Bitcoin is currently being used more than it ever has been before. Its usage per day peaked toward the end of December 2015, proving that there’s still a desire to use Bitcoin.
Beyond the average consumer, Bitcoin’s main attraction for investors is the technology behind how it works. This is known as the blockchain. WIRED explains how the blockchain works, as well as how it can be used for more than just a simple currency:
The blockchain is essentially a database running across a vast array of independent machines. With Bitcoin, it oversees the exchange of money. But it can oversee the exchange of anything that holds value, including stocks, bonds, and futures as well as houses and car titles.
Among these investors are Bitcoin startups and veteran organizations who want to use the blockchain technology to help Bitcoin transactions become easier to use. One in particular, Coinbase, a Bitcoin exchange company in San Francisco, California, is involved in developing a Bitcoin debit card, which can be used to spend Bitcoin anywhere a VISA card is accepted. The concept behind doing this is that businesses won’t have to worry about processing fees associated with credit card transactions. This might prompt companies to adopt Bitcoin as a quality payment feature in the future.
With all kinds of new developments taking advantage of Bitcoin technology, we might see a resurgence in Bitcoin’s popularity in the general public, and not just by the crooks who sell illegal goods on the black market. Maybe we’ll even see an increase in use of other kinds of cryptocurrency, including everyone’s favorite, Dogecoin-- the adorable cryptocurrency based on the derpy charm of a goofy Shiba Inu dog.

If Bitcoin makes a return, would you want to give it a shot? Let us know in the comments.


